The individual was identified by a team of researchers working undercover for Recorded Future, a company specializing in real-time threat intelligence.
He boasted of how he'd exploited a router vulnerability to infiltrate the computer of "a captain at 432d Aircraft Maintenance Squadron Reaper AMU OIC, stationed at Creech AFB in Nevada" and steal the trove of documents, and offered them up to the highest bidder.
Our research team, Insikt Group, identified a newly registered member of a hacking forum attempting to sell highly sensitive documents about the U.S. military MQ-9 Reaper drone. Read the #analysis to learn more: https://t.co/tdfSWH7eiC
— Recorded Future (@RecordedFuture) July 11, 2018
However, a lack of interest led the hacker to drop his price to US$150, and he also readily provided other forum members with samples of the files — the Recorded Future team concluded the hacker "clearly had no knowledge of how much this data may cost and where and whom to sell it to", and was "attempting to get rid of it as soon as possible".
Easy Pickings
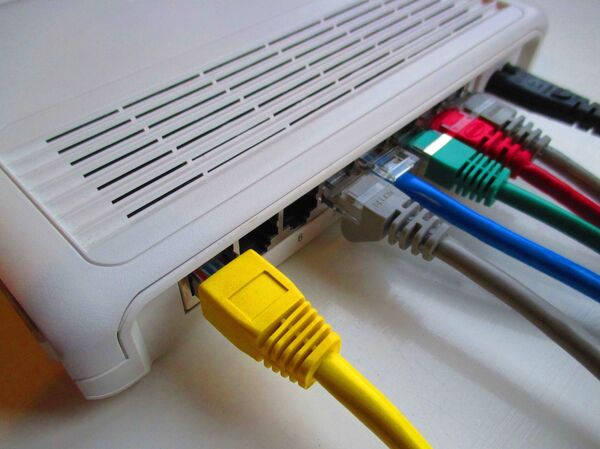
The ability of an apparently inept hacker to access highly sensitive classified US military information may shock, but their potentially devastating attack is likely to have been a matter of sheer luck. He is thought to have accessed the computer via a widely known vulnerability afflicting Netgear internet routers.
The vulnerability allows hackers to access private files remotely if a user's password is outdated — despite several firmware updates and many news articles, thousands of routers remain assailable.
Even artless hackers can exploit the weakspot by scanning large segments of the internet by country, identifying which routers have a standard port used by private servers, and using a default password to break in.
The firm's infiltrators say they have a "good level of confidence" of the hacker's identity, and are coordinating with US Homeland Security officials to assist in his arrest. It's not the first time an amateur hacker failed to cover their tracks adequately.
Making Friends and Enemies
In 2005, Samy Kamkar created the 'Samy Worm', which infected in excess of a million MySpace accounts in a mere 20-hours, one of the fastest-growing malware attacks of all time.
The virus inserted "Samy is my hero" at the end of every victim's profile — and when a user viewed an infected profile, they would also be infected, and a friend request would be automatically sent to Kamkar.
The ploy led to the temporary closure of MySpace and earned Kamkar an inordinate amount of virtual pals, but any resultant celebration on his part was short-lived — six months later, his home was raided by the United States Secret Service and Electronic Crimes Task Force, under the Patriot Act, for his efforts.
2005: The Samy worm, the first self-propagating cross-site scripting worm, was released onto the-then-mega-popular MySpace by Samy Kamkar. pic.twitter.com/OuZG1YBlJp
— Today In Infosec (@todayininfosec) October 4, 2017
He eventually accepted a plea bargain — in return for serving no time in prison, he paid a US$20,000 fine, served three years of probation, and undertook 720 hours of community service. He was also banned from owning more than one unnetworked computer, and explicitly prohibited from accessing the internet for any reason during his probationary period.
Nonetheless, when restrictions on his online activities were lifted in 2008, Kamkar was quickly up to his old tricks anew — albeit as a white hat hacker, identifying weaknesses in major businesses' digital assets for a premium. Since then, he has founded a number of start-ups and gives regular talks worldwide on digital security.
It's not merely the private sector that has expressed an interest in his work — in 2010, he released Evercookie, a web cookie that "cannot be deleted". Top-secret NSA documents released by Edward Snowden demonstrate the US spying agency was interested in the resource as a means of hacking and tracking Tor users.
Achilles' Heel
In 2006, Romanian student Eduard Lucian Mandru hacked the US Department of Defense's computer systems, using compromised servers in Japan. When inside, he infected a number of systems with an information-stealing trojan virus before deleting access logs.
Mandru's track-covering efforts were so effective investigators were stumped, their sole lead being the email address — wolfenstein_ingrid@yahoo.com — linked to the attack. Extensive searches for the identity of the account holder proved fruitless, however — that is until in 2008, when Mandru, by then unemployed, began posting his CV on local job-seeking websites. His resume included the email address, which led investigators straight to his front door in 2009.

Genius Move
In 2008, Shahee Mirza and three friends hacked the website of Bangladesh's elite security force, Rapid Action Battalion. Visitors were met with a message bemoaning the government's failure to develop information technology in the country, along with banners saying the site had been attacked by "GINIOUS" hackers.
In a less 'ginious' move, another banner boastfully identified Mirza as one of the culprits — he and his associated were arrested the very next day, and faced a decade in federal prison for their stunt.
However, Mirza et al managed to avoid a custodial sentence, and he has since gone on to become a a Certified Ethical Hacker who attacks security systems on behalf of their owners, seeking vulnerabilities a malicious hacker could exploit.
Double Agent
In 2009, Jesse William McGraw, leader of anarchist hacking group Electronik Tribulation Army, was working as a security guard at the North Central Medical Plaza in Dallas. During one of his night shifts, McGraw filmed himself conducting an "infiltration" mission at the building — soundtracked by James Bond music, he stalked deserted corridors, installed malware virus RxBot on computers, and threatening rival hacker gangs such as Anonymous. He then uploaded the video to his YouTube channel, whereupon he came to the attention of the Federal Bureau of Investigation.
While a hacker foolish enough to film themselves at work and broadcast it to the world may not seem so threatening, his hacking efforts included the installation of a ‘backdoor' in the Plaza's HVAC unit, which controlled the heating, ventilation and air conditioning for the first and second floors of the North Central Surgery Center, which could have deleteriously affected patients, or caused drugs and other medical supplies to go bad.
He was sentenced in 2011 to nine years and two months in prison, and ordered to pay US$31,881 in restitution. He will serve three years of supervised release following his incarceration.