The hysteria over the DNC hack, which escalated dramatically earlier this month after the US government hinted that it might launch cyber-attacks against Russia in retaliation, is extremely worrying, according to Carr, since it has the potential to set an important precedent.
"The entire affair blaming the Russian intelligence service for what to me seems like just an act by an individual or group of individual hackers is a huge error, and sets a very bad precedent for relations between governments," the cybersecurity analyst said, speaking to Radio Sputnik on Wednesday. "The standard of proof should be much higher before one government blames another."
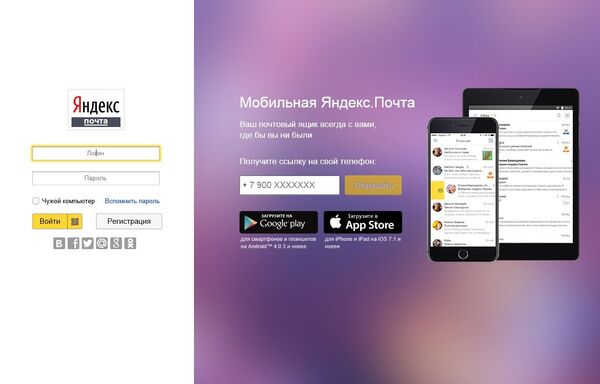
In a recent article for Medium.com titled 'The Yandex Domain Problem', Carr explained that his doubt in the veracity of US officials' charges stems primarily from the fact that the so-called smoking gun of their case, the 'spear phishing email' sent to DNC official Billy Rhinehart, uses a Yandex.com domain, not a Yandex.ru one, meaning that the hackers probably don't speak Russian.
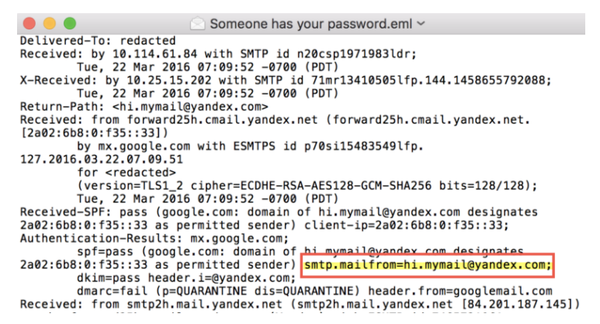
Carr told Sputnik that "there are two issues [here]: one is that it's not from Yandex.ru, which would be the easiest way for somebody in Russia to create an email address on Yandex. It's from Yandex.com, which would be more for people like me that don't speak Russian, but want to have an email address from that particular Russian company."
Secondly, Carr suggested that he found it curious why Russian intelligence would be inclined to use a Yandex domain in the first place. "Why would a Russian intelligence service use Yandex at all? In other words, why would any intelligence service anywhere in the world do a secret operation and do it from their own servers, or from a company in their own country, or use tools that have been attributed to Russian developers, or leave any other obvious clue? It just doesn't make sense."
The expert noted that it was interesting that the DNC did not present the hack as a criminal matter from the beginning (which would have allowed the FBI to lead the investigation) but chose instead to conduct a private probe using the private company CrowdStrike.
"In our country, that is what businesses do: they'll hire for profit companies like CrowdStrike to come in and do the data forensics and the incident response. What is not part of the package is to assign blame to a foreign government. That's not CrowdStrike's job, that's not my job. It's nobody's job or business except the individual government."
The most significant accusation made by the Democratic Party, and later by top US lawmakers and officials, is that Russian security services not only hacked the DNC, but released the information to WikiLeaks, ostensibly in an effort to change the course of the US election. This idea is ludicrous in and of itself, according to Carr.
"I don't think that Mr. Putin really cares who takes the office of president. He'll be dealing with whoever it is, and that's just the reality of politics and international diplomacy. But to actually mount not one, but two intelligence operations…[the idea] that literally two different Russian intelligence agencies were in the DNC at the same time and didn't know each other was there, and to use up those resources, especially during a time when one of those agencies – the GRU [military intelligence] was going through a lot of changes over the past few years…and to do it when one candidate has almost zero chance of winning, the whole thing is just ludicrous."
What worries Carr the most is the precedent that has been set here. "On the basis of extremely weak, in some cases non-existent evidence, the US government has formally accused the Russian government of this activity. That sets the bar very low when it comes to establishing state control over non-state actors."
"This could turn around and hurt the US government later because another country could say 'we are now accusing the US government of doing something on the basis of very weak evidence…' We've really created a dangerous precedent here, and I'm hoping that at some point in time, this gets reversed or at least is acknowledged as something that should not be considered as a precedent in international law."
"The bottom line here is that there is already a great deal of tension between the Russian government and the US government over matters that have nothing to do with the Democratic National Committee or the US election. My fear is that individuals, whether they are Russian-speaking or not, have taken advantage of this to create even further tension between these two governments. We really cannot afford any further tension," Carr stressed.