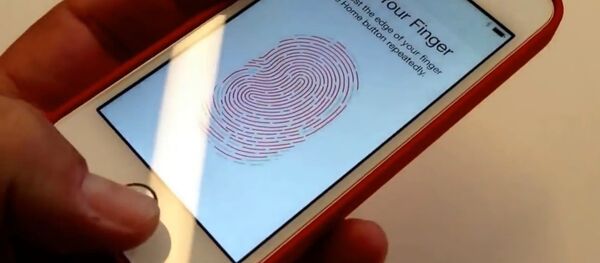
Earlier this year, the researchers completed their project "DeepMasterPrints," which uses machine learning to become a skeleton key of sorts for biometrically secured property. The researchers say DeepMasterPrints can unlock about one-third of smartphones secured in such a way.
Smartphones aren't the only kinds of devices that would be vulnerable to such cracking methods — airlines and car rental companies have begun implementing biometrics, and Mastercard has also weighed using it. Some safes and padlocks also use fingerprinting technology.
"Phones and many more devices don't capture your entire fingerprint," the researchers told CNBC. "There's not enough space on the device, so they capture a partial fingerprint — which is not as secure as the full image. [People assume] the device stitches images of their fingerprint together, but that's not really what happens — it keeps sets of partial fingerprints."
While the researchers' project has made the vulnerabilities of biometrics immediately clear, DeepMasterPrints "requires physical access to the phone," web developer and technologist Chris Garaffa told Sputnik News.
"This development is concerning, but in the immediate term, it's not something that most people need to be concerned about. At the point that a sophisticated attacker has physical control of a phone, it's fair to assume that the phone has been compromised in one of many ways and cannot be trusted to be secure anymore — even without having fingerprint-enabled access," Garaffa noted.
Technology such as Cellebrite, Israeli technology that plugs into a phone and infiltrates its data — including messages sent over encrypted applications like Signal or WhatsApp — can be used by authorities in the US to get into suspects' phones, bypassing many security measures.
Even still, biometrics are in many ways less secure than traditional passwords or patterns used to lock phones. "People who have heightened security concerns — for example, journalists and activists — should not use biometric authentication and instead secure their phones with a long password, and ensure that it's never out of their physical control and never plugged into an unknown computer or charger," Garaffa told Sputnik News.
Judges in the US have previously ruled that police cannot compel Americans to unlock their phones with a password but are allowed to compel people to provide their fingerprints for such purposes. The issue is further compounded by the massive stockpiles of fingerprints in the hands of US authorities, with more than 31 million in a Department of Homeland Security biometrics database as of 2014 and more than 34 million belonging to civilians also in an FBI database as of 2010.