In an official statement, the FBI said the virus — ‘VPNFilter' — was being used to launch attacks on infrastructure and render electronic devices useless. Anyone possessing a router is strongly urged by the Bureau to reset their device — the malware works in three stages, and rebooting the router prevents the implementation of the latter two stages.
"Owners are advised to consider disabling remote management settings on devices and secure with strong passwords and encryption when enabled. Network devices should be upgraded to the latest available versions of firmware," the Bureau suggested.
‘Advanced State Actors'
The vulnerability was first made public May 23 by networking hardware developer Cisco — the company claimed it'd been spreading since 2016, although over the prior fortnight the number of attacks had "ramped up."
"VPNFilter is an expansive, robust, highly capable, and dangerous threat [targeting] devices challenging to defend. The destructive capability particularly concerns us. This shows the actor is willing to burn users' devices to cover their tracks. If it suited their goals, this command could be executed on a broad scale, potentially rendering hundreds of thousands of devices unusable, disabling internet access worldwide or in a focused region where it suited the actor's purposes," the firm said in a blog post.
Similarly, the FBI didn't point fingers at a particular group or nation as being behind the hostile strategy. However, media reporting on the topic has almost universally blamed Russian hackers — whether acting with state sponsorship or not — without attribution.
While the meme of omnipotent Russian hackers has been a recurrent one in the Western mainstream, supporting evidence has been scant. Conversely however, evidence of Western intelligence agencies employing sophisticated hacking techniques, and creating malicious software to attack citizens, is ample.
Homegrown Viruses
For instance, as part of its ‘Vault 7' series of exposures, whistleblower organisation WikiLeaks revealed how US Central Intelligence Agency contractor Raytheon Blackbird Technologies helped the CIA's Remote Development Branch (RDB) to collect ideas for developing their own advanced malware projects — and how the CIA's UMBRAGE malware development teams also borrowed codes from publicly available malware samples to build the Agency's own spyware tools.
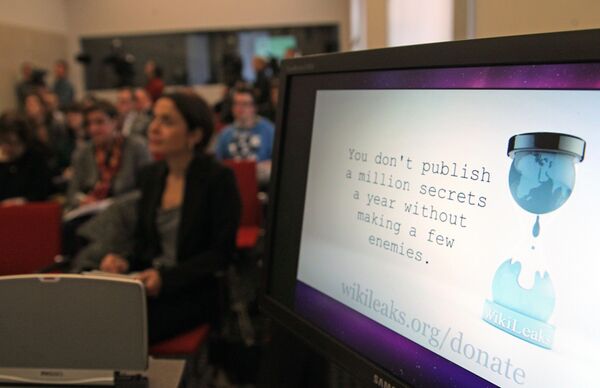
The Vault 7 exposures also documented a series of virus implants apparently concocted by the CIA itself, much of which was targeted at consumer tech. For instance, ELSA tracked the geo-location of targeted PCs and laptops running Microsoft Windows, while Pandemic allowed the Agency to turn Windows file servers into covert attack machines capable of silently infecting other computers inside a targeted network, and Athena even allowed the CIA to full control over infected Windows PCs remotely — it worked against every version of Microsoft's Windows operating systems, from Windows XP to Windows 10.

Finally, and perhaps most notoriously of all, the Weeping Angel spying tool allowed the agency to infiltrate smart televisions, transforming them into covert microphones.





