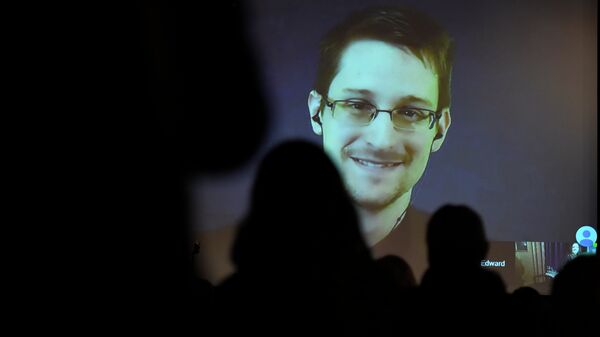
In June 2013, Edward Snowden famously leaked thousands of sensitive classified documents to reporters, revealing the extent and scale of mass surveillance programs in the US and UK.
The exposures sparked major public debate over government surveillance, privacy rights and data protection, which have barely abated since.
Shortly after the story broke however, the Red Team, directed by then-Marine Corps Captain Robert Johnston, sent out phishing emails to 5,000 military staff to test out cybersecurity standards. The phishing email included a malicious link for unsuspecting users to click on and it then installed malware.
The subject of the email read:
"SEAL team six conducts an operation that kills Edward Snowden."
The phishing attack was so effective they "had to shut down the operation" due to the significant click-through rate, which was "through the roof," Johnston said.
There was a time I'd have been surprised the government writes fan fiction about murdering its critics. https://t.co/js0wWKZW5a
— Edward Snowden (@Snowden) November 9, 2017
Red Teaming
Johnston led the Marine Corps' newly-formed Cyber Protection Team 81 as part of the military's Cyber Command, Cybercom.
"[Red teaming] means looking at ourselves and our way of doing business. A red team may play devil's advocate or Napoleon's corporal in order to outrate the enemy. Although sometimes adversarial, it is not intended to be negative in nature. The general idea can be described as a bright light we shine on ourselves to expose areas where we can improve effectiveness. This light starts out white for everyone under the banner of red teaming, but it goes through the prism of the particular organization and takes many different forms in its application," the Marine Corps state in a 2012 publication.
After leaving the Marine Corps later in November 2015, he joined CrowdStrike, the cybersecurity firm that subsequently investigated the hacking of Democratic National Committee (DNC) emails in 2016. The organization's resultant report was widely ridiculed.
Johnston left CrowdStrike in July 2016 to establish his own cybersecurity firm, Adlumin, in Washington DC.
Snowden's Future
As of November 2017, Snowden remains an asylum subject in Moscow, Russia. If extradited to the US where he could face up to 30 years in prison, under the Espionage Act of 1917.
Here's what happened when we delivered thousands of your messages of support to Edward @Snowden. Your words are powerful. Please take part in #WriteForRights and send a message of hope https://t.co/pNucCt2X7g pic.twitter.com/iRx5IiLwVL
— Amnesty UK (@AmnestyUK) November 9, 2017
Many privacy rights advocates and supporters have called for Snowden to be pardoned or extended leniency on moral grounds, arguing his actions, even if illegal, were not for personal benefit but in order to effect change and reform.
Western government officials, military service members and mainstream media journalists think otherwise, however, arguing he betrayed the US and endangered national security by divulging the government's surveillance practices.