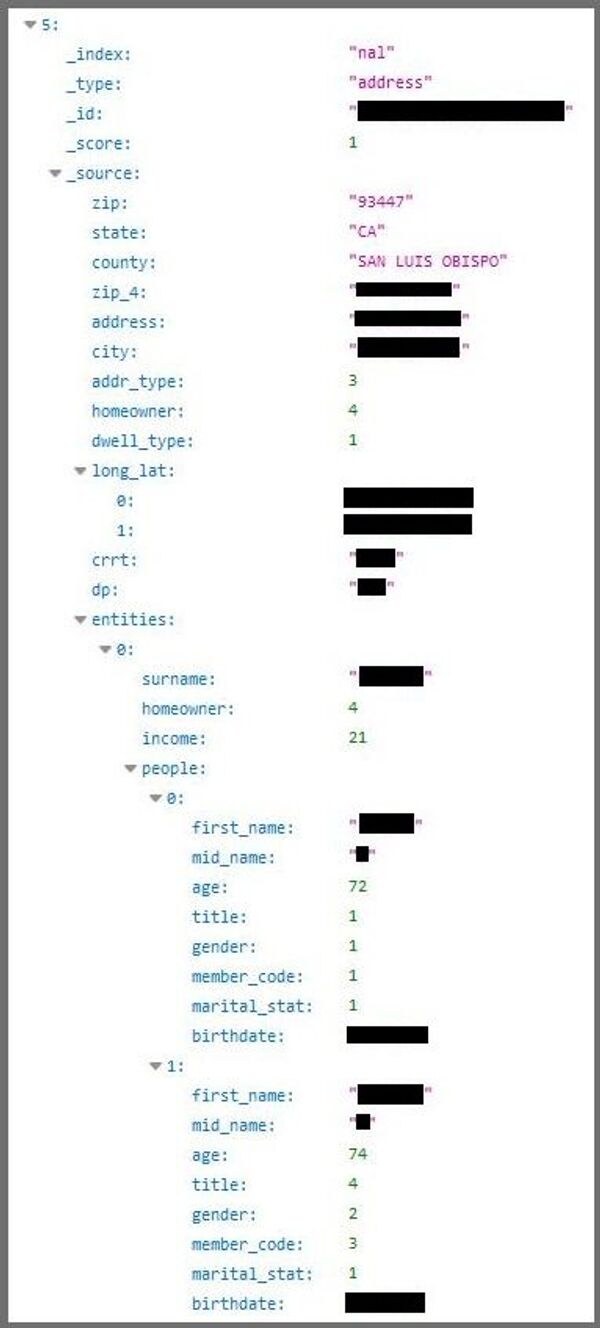
The 24-megabyte database includes names, ages and genders, as well as income levels and marital status, with some information coded and others left in plain text. However, it didn't include payment information or Social Security numbers, CNET noted.
"I wouldn't like my data to be exposed like this," Rotem told CNET. "It should not be there."
A Microsoft spokesperson told CNET Monday, "We have notified the owner of the database and are taking appropriate steps to help the customer remove the data until it can be properly secured." The database was hosted on one of the company's servers.
"Keeping this information online without a password, first of all, should be criminal," web developer and technologist Chris Garaffa told Radio Sputnik's Loud and Clear.
"The scariest thing about this is, we have no idea where this data came from yet," Garaffa said. He told hosts Brian Becker and John Kiriakou that the majority of people in the database are over 40 years old. "So this is likely [coming from] a service used by people who are generally over 40 years old.
"But there are many of those," Garaffa said, noting some likely contenders were a dating app, an insurance firm or a mortgage company.
"This could be an advertiser target database," he noted, "focusing on people over 40, maybe have a certain level of income, or delivering ads to people who own or rent" a house.
If they want to plug the leak, though, the technologist said, "you're going to have to look at who rents this server space from Microsoft. Unfortunately that could be [paid for] using a stolen credit card; that could be a completely fake name, a prepaid card used to pay for it. But then you have to start looking and doing some forensics on who is in this database, and hopefully, I would hope that a company could figure out, ‘This looks like our information,' and come forward and say, ‘Yes, this happened to us.' Unfortunately, that would probably hit their bottom line pretty hard, and I don't expect whatever company it is to do the right thing."
"Researchers are already doing digital forensics on the leak itself," Garaffa said, noting that "Microsoft will have to cooperate," because it has essential information about the renter's identity. However, he said it's still far too early to discuss any kind of legal action.
"At this point, anyone who pays any sort of attention just has to realize that hosting any information like this on the internet requires somebody who is focused on security, who is knowledgeable about security. I don't think there's any excuse for any company storing any sort of personal information, including names, addresses, payment information, whatever it is, to not have a person or a team focused on security and doing regular audits, and doing regular work to keep things safe," Garaffa said.
"And again, we don't know if this is the original source of a company that's using this information, or if this is information that was hacked by somebody else or breached by somebody else and stored on this server. We still don't know that. Either way, though, this is not acceptable."
Garaffa said researchers found the database by using software that "hits basically every address on the internet, one by one, and checks it for what kind of server it is running, how old is that server, does it have any old software that is open to vulnerabilities… they unleashed it on the entire internet and found this database up there."
"It's very easy to do this, it just takes time — and if you have a lot of computers, it takes a little less time. The internet is a big place, so researchers are constantly scanning, constantly looking to see what they can find in treasure troves of personal information like this," Garaffa said.
The web developer warned that, now that the database is out there, "people are going to be targeted for spam and other bad email campaigns, overall just spam, viruses in emails, things like that, based on the fact that a lot of people's email addresses are just their first name-last name at Gmail or Yahoo or whatever, so it's easy to write a little program to just go through all of this and put it out."
"Also, once you have someone's name, address and birthday, it can be easy, depending on who you're talking to, to take over, for example, a cell phone account or potentially even a bank account. There's something called ‘social engineering,' which is a way hackers will try to convince an agent — may be a bank teller or the phone agent at your phone company — to take over the account. You forgot what credit card you used, so you can't confirm that information, but they tell a sob story about that. So people are going to need to regularly check their credit scores; people are going to need to regularly check any online accounts they have to make sure that all the activity actually belongs to them," Garaffa said.