The report Technology Briefing Series: Child Sexual Abuse Imagery by Demos, published on January 22, stresses that smart digital devices provide a platform for sexual predators.
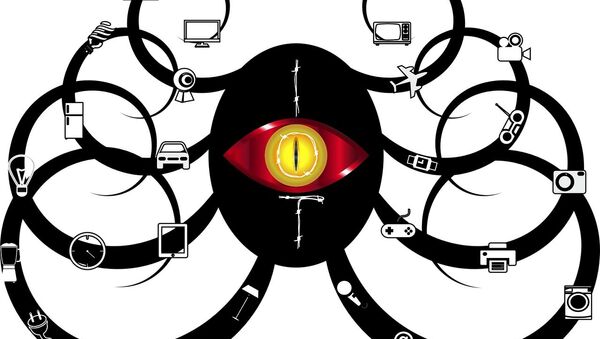
As our homes become more technologically sophisticated, one of the emerging trends named by Demos researchers is IoT creating new opportunities for sex offenders and the risk is set to grow in the coming three to five years.
"Unsecured 'Internet of Things' devices (such as a 'smart' TV) acting as 'safe' repositories of images, without the knowledge of the device owner" — this part of the report is posed to raise privacy and security concerns among users. On the bright side, the IoT — due to its extensive applications — has the power to rapidly increase productivity and change lifestyles. So, how dangerous the IoT really is and could its disruptive potential be exaggerated?
.@Demos is launching their Tech Education Project on Monday — a new series of briefing papers & workshops aiming to start new conversations about risks in the online world. The first paper deals with the issue of child sexual abuse imagery online. https://t.co/O6TOa5YXRV pic.twitter.com/o26LTf677o
— IWF Hotline (@IWFhotline) January 20, 2018
According to Fred Langford, deputy CEO of the Internet Watch Foundation, which worked with on the report, cyber-savvy pedophiles could "scan" for vulnerable devices anywhere in the world and store their illegal images there. He warned that it opens households to investigation by police, who may believe the abuse photos belong to them given they are stored on their devices.
Whose Responsibility?
In this case, resilience and responsibility are key for both users and the developers of IoT technology. However, it is easier said than done, according to Dr. Mariarosaria Taddeo, Researcher Fellow at the Oxford Internet Institute and Deputy Director of the Digital Ethics Lab. Identification of users is an important step but is up against protection of privacy of these very users, she told Sputnik.
The developers are faced with the high cost of ensuring security on IoT devices and the risk of slowing down the production, as more time is required to install appropriate digital protections, whether it is a pacemaker or a remotely controlled thermostat.
"Guaranteeing security is an effort that producers have to make but only now learning to make it. Security comes at costs that providers need to face," Dr. Taddeo told Sputnik.
In 2017 the US Federal Bureau of Investigation (FBI) advised parents to safeguard security checks on IoT toys, citing "the rush to market them and to make them easy to use" as one of the reasons for safety breaches
READ MORE: FBI Warning: Watch Out Parents, Internet-Connected Toys Are Dangerous
Nature of Risk Unchanged
However, it is not all bad, as IoT provides various opportunities to simplify livelihoods and improve business efficiency.
While the IoT is constantly developing, the risks it poses aren't drastically unlike those of more common devices that can be as vulnerable to sex offenders as any other technology. So what is new in threats posed by the IoT?
"To some extent the risks are not that different from the ones posed by a mobile phone, laptop or a computer. What changes is the pervasive nature of the risks: the moment you are using not just your computer or mobile phone but also your toaster, thermostat or a doll for your daughter, or a pacemaker — the opportunity for the risk to become a threat multiplies. The nature of risk remains the same," Dr. Taddeo told Sputnik.
Borderless Issue
The report by Demos also stresses that the task of tackling child sexual abuse images is inherently difficult, since the cyberspace "has allowed for new channels of access and distribution that are often based overseas and change frequently with technological advance."
Dr. Bernard Gallagher, Reader in Social Work and Applied Social Sciences, at the University of Huddersfield, is also of the opinion that there are restrictions on what law enforcement can do. That said, he told Sputnik, "a lot of international law enforcement cooperation is going on. Police in America, for example, might detect offenders and pass those details to the host nations, where the perpetrators are located."
Within the European Union, the General Data Protection Regulation (GDPR) which will unify data protection for all individuals in Europe, is to be launched on May 25, 2018. According to Dr. Taddeo it is a "major step forward in security of IoT devices." However, mass data retention in the EU has also caused a stir among human rights NGOs.
READ MORE: Despite Court Rulings, EU's Unlawful Mass Data Retention Policies Remain
The United Kingdom will comply to GDPR, despite leaving the European Union on March 29, 2019. The GDPR will replace the data protection directive (officially Directive 95/46/EC)[2] of 1995.
The views and opinions expressed in the article are those of the speakers and do not necessarily reflect those of Sputnik.