In an online statement, the Shadow Brokers group said that beginning in June, they will release software to access secret spying tools, which would give anyone willing to pay the ability to break into phone handsets, network routers and web browsers on some of the most popular consumer devices.
The hackers said that they would also be selling zero-days, secret vulnerabilities that could be used to break into Windows 10. Without revealing many details, the group said there may in addition be a dump of data from nuclear and missile programs in Iran, China, North Korea and Russia.
They also will supply data from international banks that use the SWIFT international money transfer network.
As researchers investigate the source of the attack, there is some indication that North Korea may have been involved.
Though evidence is inconclusive, a portion of the code used in an early version of the “WannaCry” malware shares a tool with a hacker group called Lazarus, which some believe has North Korean government connections.
"This implies there is a common source for that code, which could mean that North Korean actors wrote WannaCry, or they both used the same third-party code," Fidelis Cybersecurity threat research manager John Bambenek told the Washington Post.
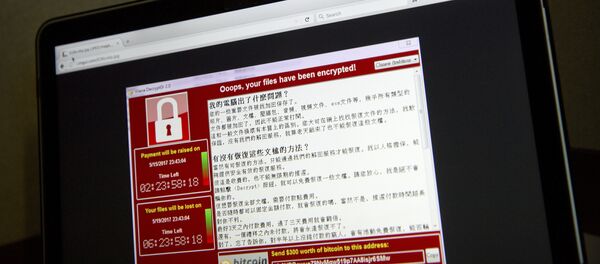
The "ransomware" infected computers’ encrypted files, effectively making them inaccessible, and presented a window demanding $300 in Bitcoin to regain access.
The Symantec software company published a blog about the potential links, saying, "While these findings do not indicate a definite link between Lazarus and WannaCry, we believe that there are sufficient connections to warrant further investigation."
On Monday, White House homeland security adviser Thomas Bossert told a briefing that the source of the attack is still under investigation. "That's the attribution that we're after right now,” he said. “It will be very satisfying for me and for all of our viewers, I think, that if we find them that we bring them to justice…. I don't want to say we have no clues…. The best and the brightest are working on that."
This incident also reignited debate over government stockpiles of vulnerabilities, with Microsoft President and Chief Legal Officer Brad Smith noting on his blog, “We have seen vulnerabilities stored by the CIA show up on WikiLeaks, and now this vulnerability stolen from the NSA has affected customers around the world.
"Repeatedly, exploits in the hands of governments have leaked into the public domain and caused widespread damage."
While studying "WannaCry," researchers found potential links to the 2004 hack of Sony Pictures that was attributed to Pyongyang, as it occurred shortly before the release of "The Interview," a satirical film based around a conspiracy to kill North Korean supreme leader Kim Jong-un.